Read the most recent articles
The world is changing more rapidly than ever.

Navigating Security Upgrades: Critical Insights from Global Trends
Critical Concerns for Security & Physical Access Control from Global Trends In an era marked by unprecedented technological advancement and evolving security threats, ADVANTIDGE works to ensure the safety and security of public and private institutions which has become an increasingly complex challenge. The digital age has ushered in a new frontier of security vulnerabilities,… View Article
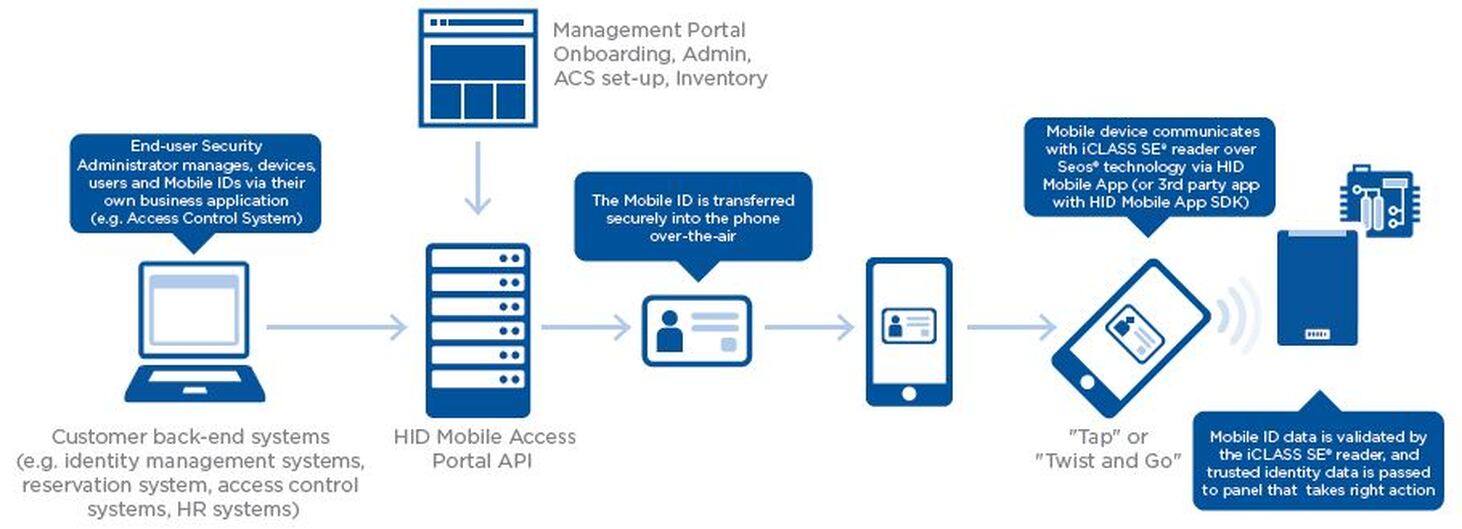
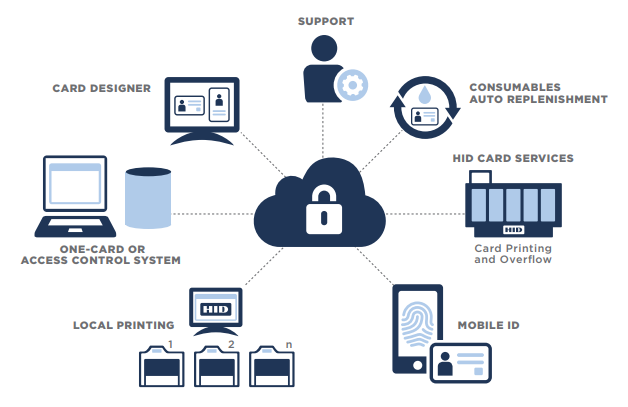
HID Origo Management Portal for Mobile Access Credentials
Announcing Enhanced Features for HID Origo Management Portal for Mobile Access Credentials ADVANTIDGE, a leading provider of secure identification solutions, is proud to announce significant updates to the HID Origo Management Portal, enhancing the control and security of physical access systems utilizing HID Mobile Access credentials. These updates introduce new features aimed at streamlining management… View Article

CCW Card Issuance: A Guide for Law Enforcement Departments
Helping Law Enforcement Departments Navigate New Requirements for CCW Card Issuance As a trusted partner in security identification solutions for over two decades, ADVANTIDGE understands the critical importance of adapting to evolving regulations and standards, especially in the realm of law enforcement. In 2024, the California Department of Justice (DOJ) implemented new requirements under Title… View Article

Entrust Sigma Card Printers for Secure ID Badge Issuance
The Advantages of Entrust Sigma Card Printers for Secure ID Badge Issuance In today’s dynamic world, the need for secure identification is paramount, especially for large organizations that handle sensitive information. Government agencies, public and private corporations, consistently seek cutting-edge solutions to issue secure ID badges. ADVANTIDGE, as an authorized reseller for Entrust technologies, recommends… View Article

HID Card Reader Upgrades with Bluetooth to Modernize Legacy PACS
Enhancing Legacy Access Control Systems: Tech Tips for Upgrading HID Card Readers with Bluetooth In the ever-evolving landscape of access control systems, ensuring the security of your organization is paramount. For many businesses still relying on legacy HID iClass readers with low-frequency 125KHz proximity cards, the vulnerability to counterfeit credentials poses a significant threat. In… View Article

Modernizing Fishing Licenses with Secure ID Credentials for Caribbean Government
Overview: Shortly after the pandemic, an east coast security integrator catering to government clients, sought out ADVANTIDGE for support in creating a comprehensive solution for upgrading the issuance and management of fishing licenses in the Caribbean. The government department managing these credentials was responsible for protecting a critical industry. With regular encounters from law enforcement,… View Article

Choosing a High-Volume ID Card Printer in 2024: The Power of Enterprise-Level Printing
The needs of large enterprises have always been diverse, yet with an overarching requirement for efficiency and quality. Especially in 2024, where ID security is more paramount than ever, businesses can’t compromise on the ability to issue high quality ID cards. The importance of investing in a high-volume ID card printer solution designed to cater… View Article

Why Does an Organization Need Custom Security ID Cards?
In today’s fast-evolving world, security stands paramount for organizations across the globe. Beyond traditional locks and keys, the demand for modern security solutions has ushered in an era where a custom security ID card plays an indispensable role. In essence, a custom security ID card is more than just an identification tool; it is an… View Article

IDP Card Printers: Unpacking The Best Warranty In The Security Industry
Industry Best Warranty: IDP Card Printers As large corporations seek to upgrade to more reliable ID card printing systems, the IDP Smart series emerges as a formidable choice. In this review, we’ll delve into the main benefits of the IDP Smart 51, Smart 70, and Smart 81 card printers, exploring how these cutting-edge solutions can… View Article

The Imperative for Upgrading Physical Access Control Systems
Upgrading Physical Access Control Systems For Security & Efficiency In an era where technological advancements are reshaping every aspect of our lives, the importance of upgrading physical access control systems cannot be overstated. Legacy systems, often relying on low-frequency 125KHz prox cards and key fobs, have become susceptible to security breaches, posing significant risks to… View Article